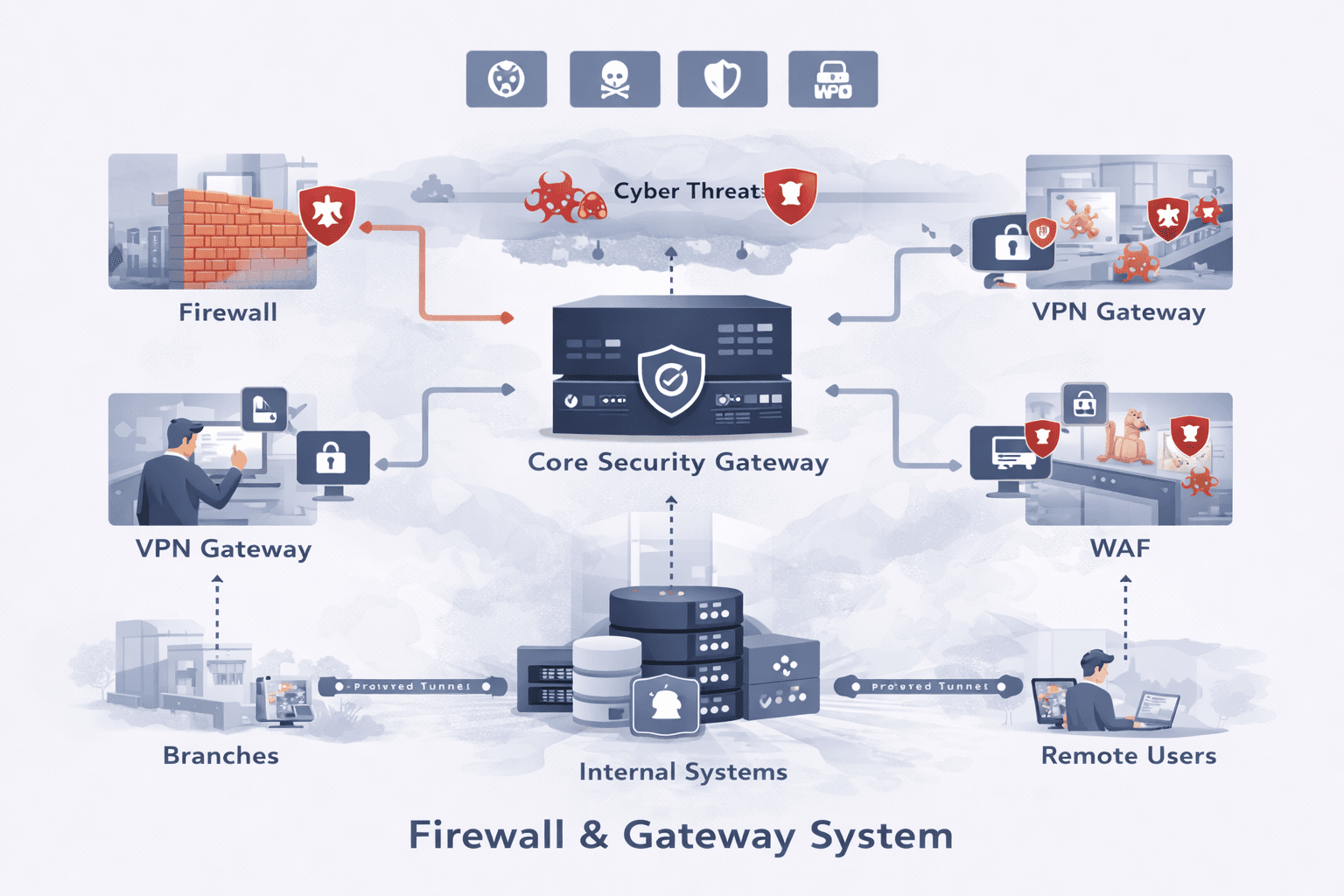
Firewall and Gateway Systems to Protect Business Networks
Every business depends on the internet to communicate with customers and store important information. With increased digital use comes increased cyber threats. A proper Firewall and Gateway System protects the entire network by blocking harmful traffic and keeping connections safe.
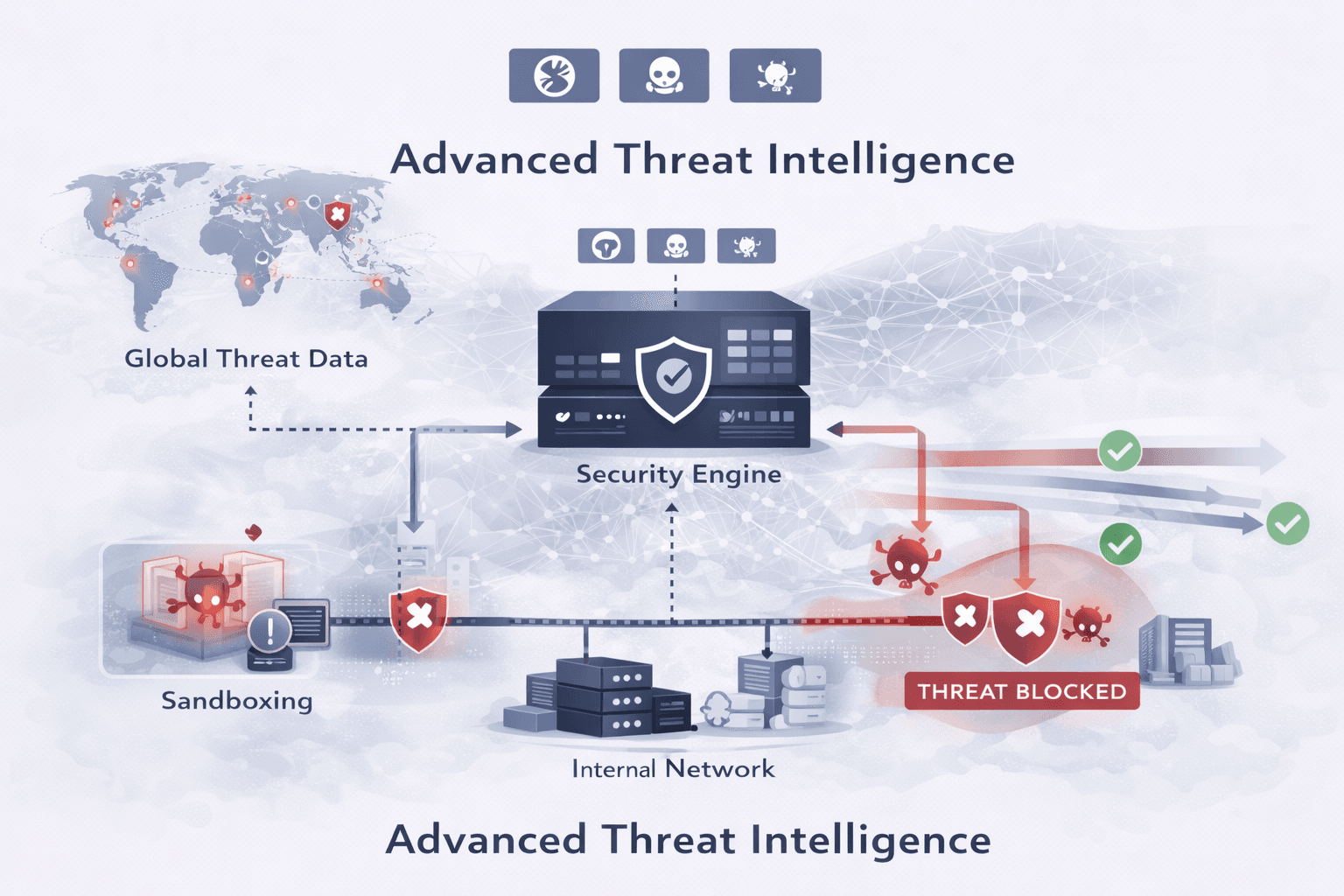
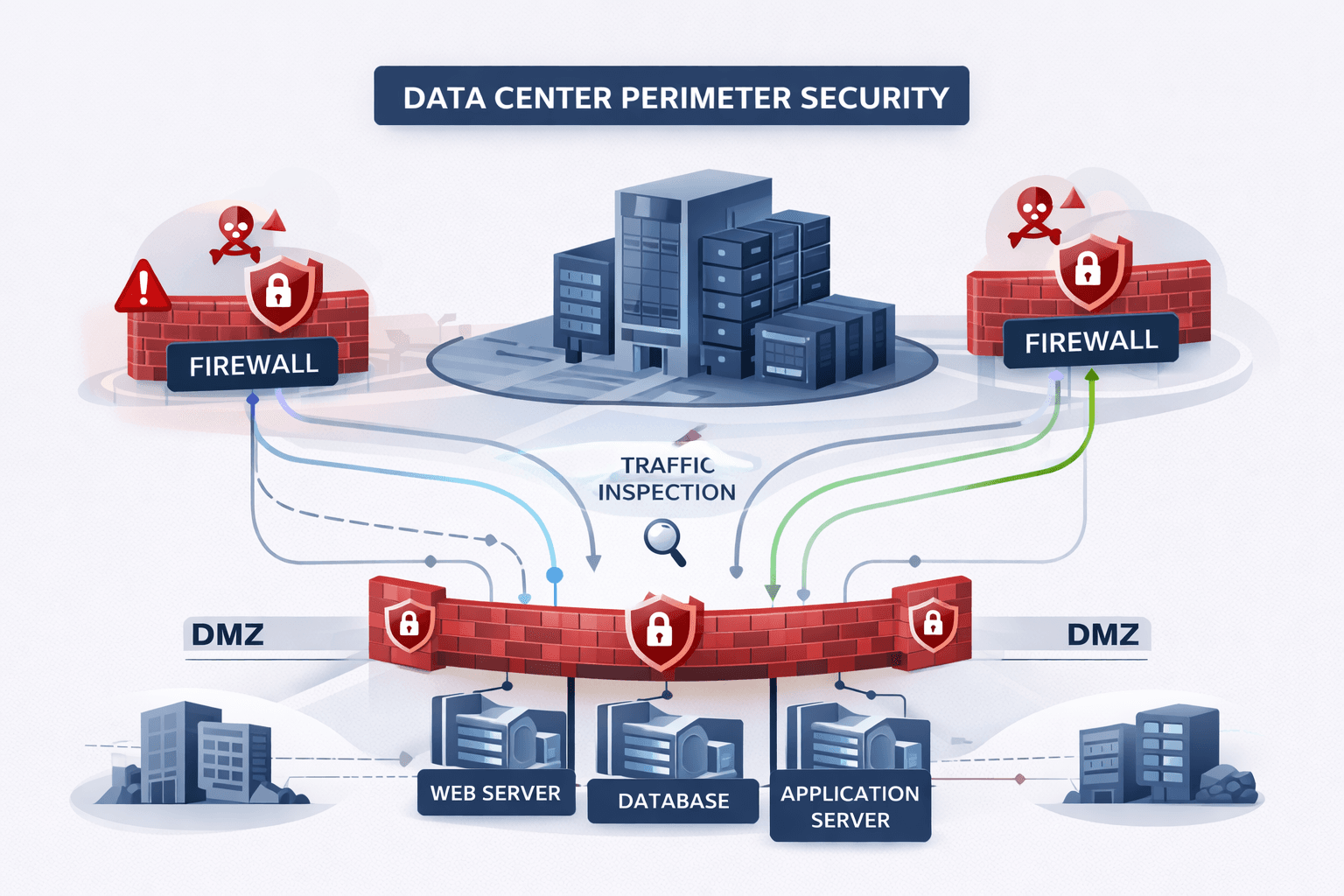
Greater Protection Against Online Threats
Threats like malware, phishing links, and SQL injections target systems with little protection. Firewall systems check all requests and only allow trusted activity, reducing risks and keeping sensitive data safe.
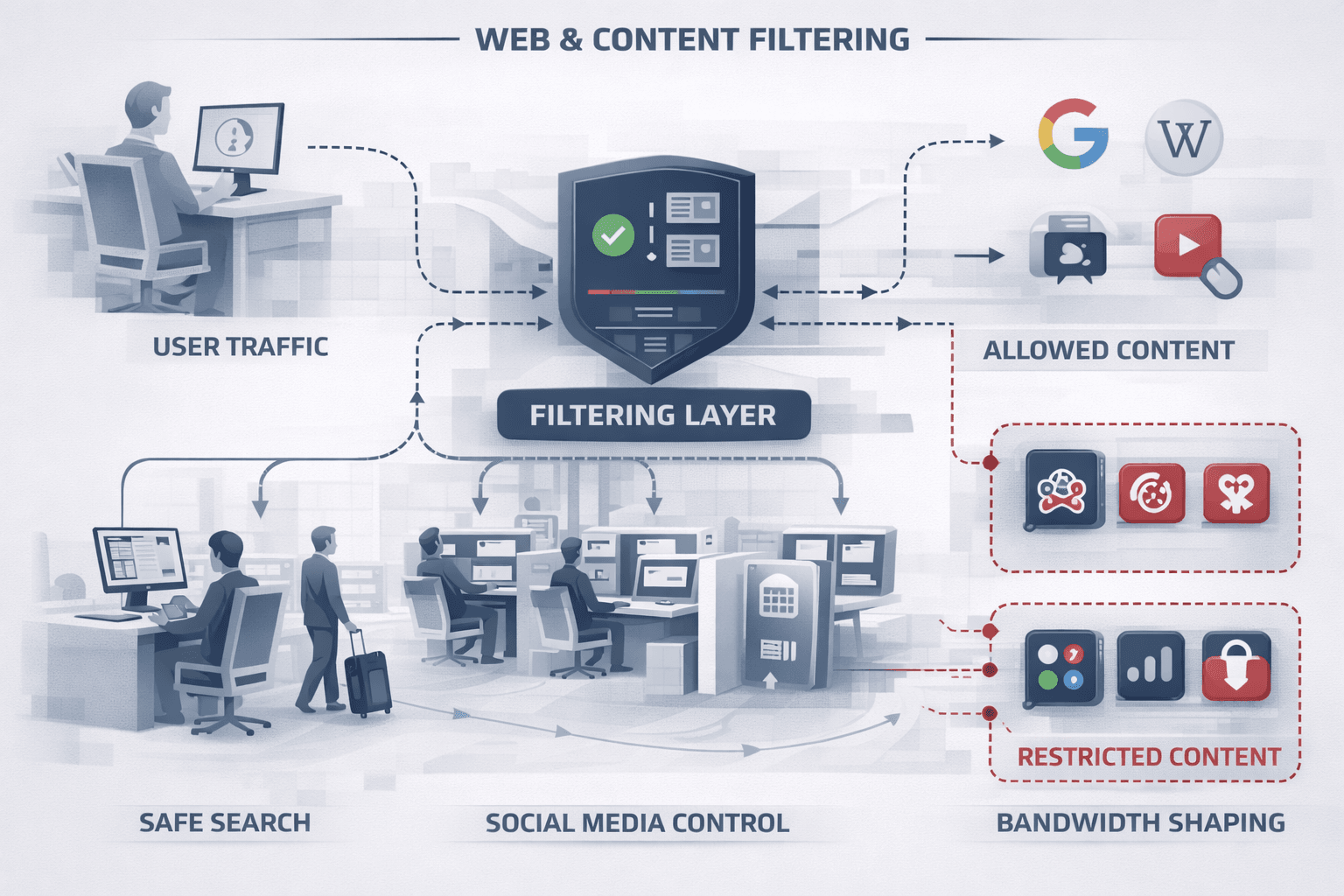
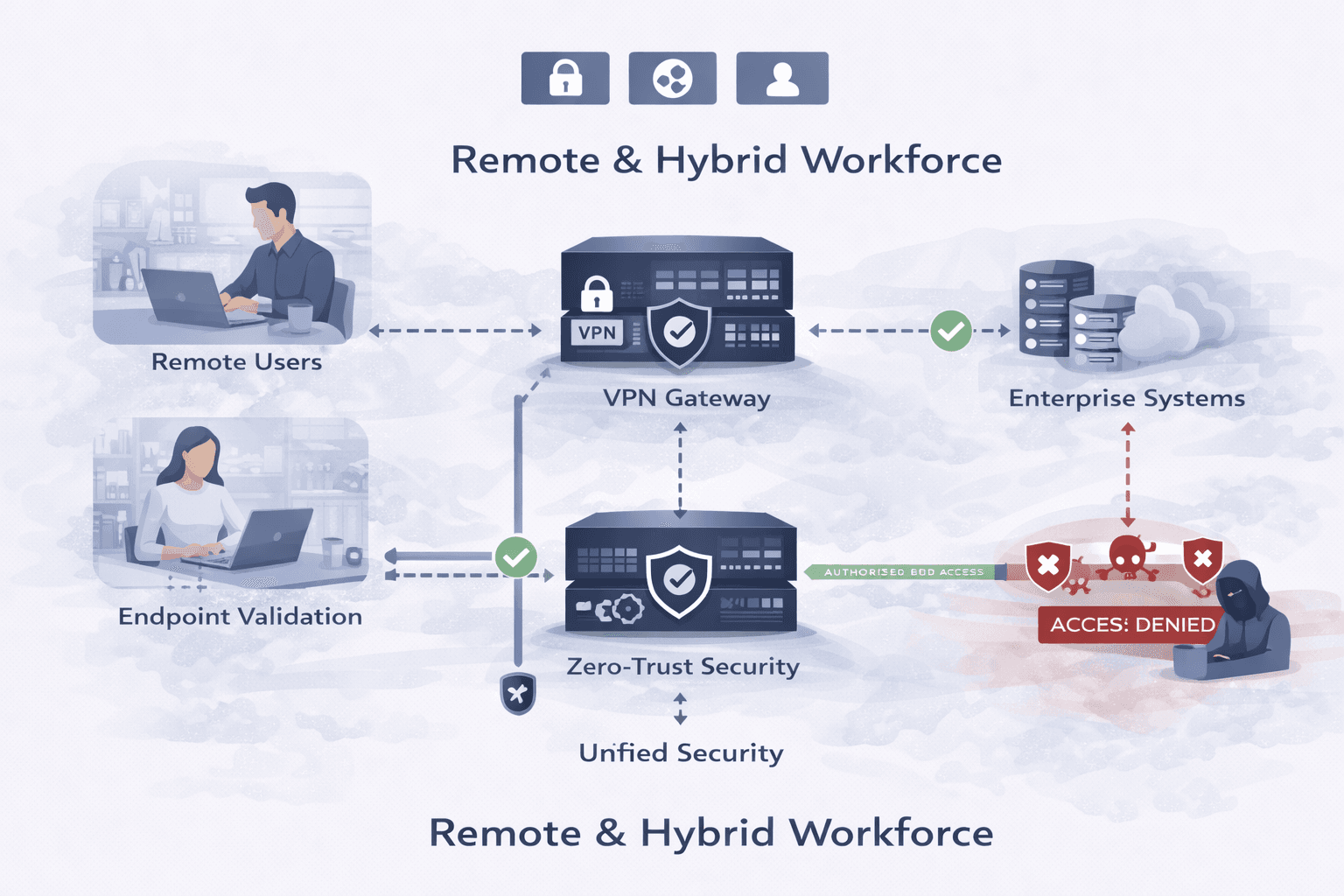
Smooth Internet Control for Increased Productivity
A gateway system helps control internet use in the office. Businesses can block risky websites, set bandwidth controls and clear rules for staff, allowing the network to be faster and more productive.
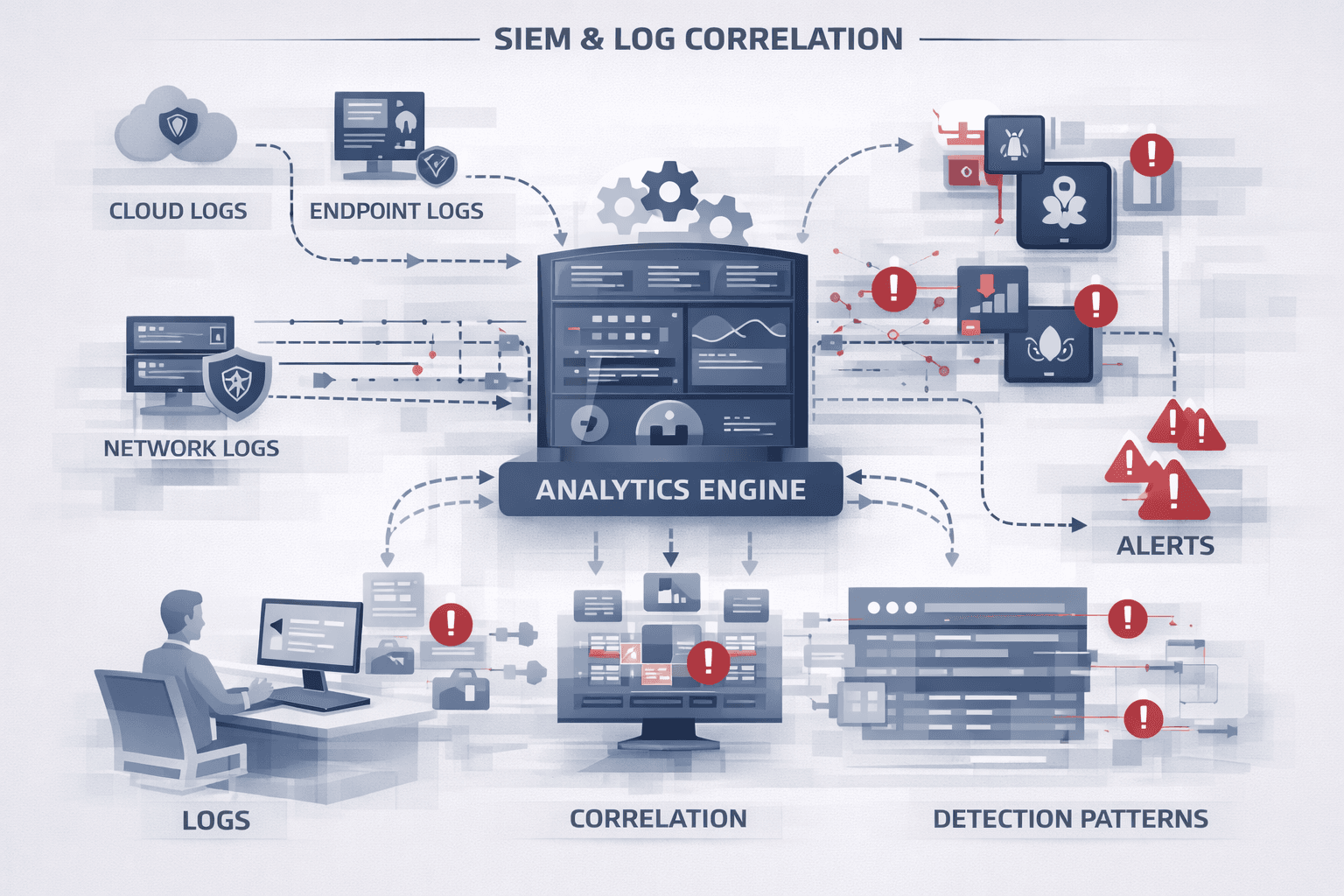
Real-Time Monitoring and Immediate Alerts
Modern firewalls provide updates and alerts when something unusual happens, helping businesses react quickly and avoid vulnerability. With constant monitoring, threats are caught before they become serious problems.

.png)